HIGH-SPEED DATA
The use of real-time data in underground mining has moved beyond the point of being a “nice to have” and is now essential for any operation looking to improve productivity or promote maximum health and safety.
Whether it is monitoring the atmosphere for harmful gas or particulates, monitoring the structural integrity of mine entries and work areas, monitoring operators’ proximity to heavy machinery or even monitoring the health and vital signs of individual workers, the use of data has become prolific within today’s mining industries.
But as the reliance on data and real-time information has soared, the ability to transfer this data across the entire mining environment, in real-time, has also increased and it is this infrastructure creation and maintenance which has become a real focal point in modern mining.
In this blog we examine how the trend of real-time monitoring, telemetry and remote activity reporting in mining has made the industry more data reliant, and the challenges of creating the infrastructure to support this level of data transmission.
ENVIRONMENT AND STRUCTURAL MONITORING
Ensuring miners are working within a safe space has always been a vital factor in underground mining, given the confined and often unpredictable nature of the work environment.
Being able to monitor these environments in real time, and receive early warning alerts of potential danger, has now become integral to any operation.
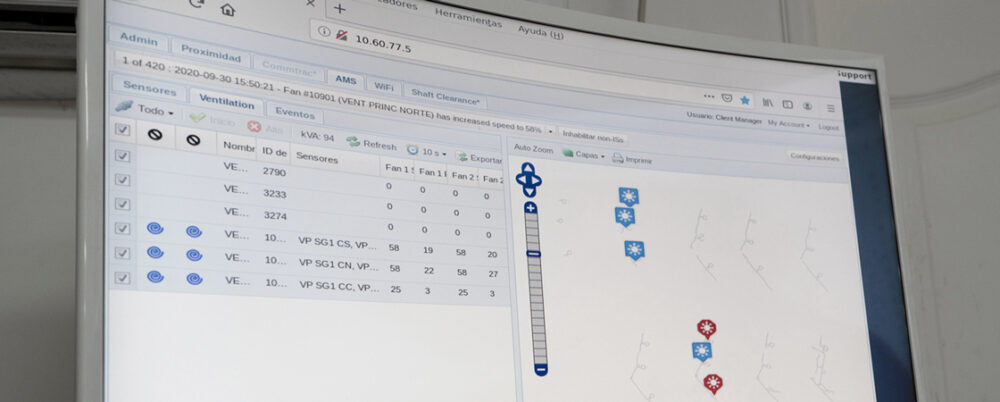
Whether it is monitoring the atmosphere for the presence or changing levels of gas or dust, measuring the air flow for adequate ventilation or testing the structural integrity of the mine roof, real-time mine-monitoring ensures that mine operators stay ahead of trends and potential problem areas.
Data can be collected in active work areas as well as in isolated and unexplored areas. This information can assist in proactive planning.
PROXIMITY DETECTION
As well as the dangers of roof falls and the sudden presence of harmful gas or dust, having workers within close proximity to heavy mobile equipment is one of the primary dangers in mining.
Historically there was nothing that could be done to reduce this risk other than proper training on safe work practices, but today, proximity detection systems that can alert personnel when they enter dangerous areas, or get within a certain distance of a machine, are providing a new level of safety.
While the presence of proximity detection systems with warning alarms offers significant safety benefits for workers on the job, there are also data reports generated that can be transmitted from the system to the surface to give mine operators a clear picture of work practices underground, and to help them identify areas of concern.
CREATING THE INFRUSTRUCTURE
Although fiber has become a popular choice for digital information networks it also comes with an array of challenges. It is expensive, inflexible, requires a separate power source, needs to be maintained or serviced by someone with specialized training, and is susceptible to damage due to its brittle nature.
All this adds up to a costly, high maintenance network.
As an alternative, some operations are turning to DC powered coaxial cable and Ethernet connections, either to supplement parts of a fiber network, or to use as an alternative.
Within a busy, robust and fast paced environment when the uptime of data transfer is most important, these coaxial cables can provide a much more effective network than fiber.
These “Power-over-Ethernet" networks remove the need for external power sources, because the power travels across the coaxial cable. Coax can also be maintained by on-sight personnel, without the need for specialized certifications – further reducing costs.
Coaxial cables are much more robust than fiber and less susceptible to breaking, making them ideal for use in underground mining. They can also be interfaced with existing fiber networks, eliminating the need for costly network replacements.
Also, because coaxial cables can be easily cut or spliced to any length, they are far more flexible to use than fiber, allowing mine operators to place end-point devices where they need them – rather than where the network dictates.